Why Choose Xcitium
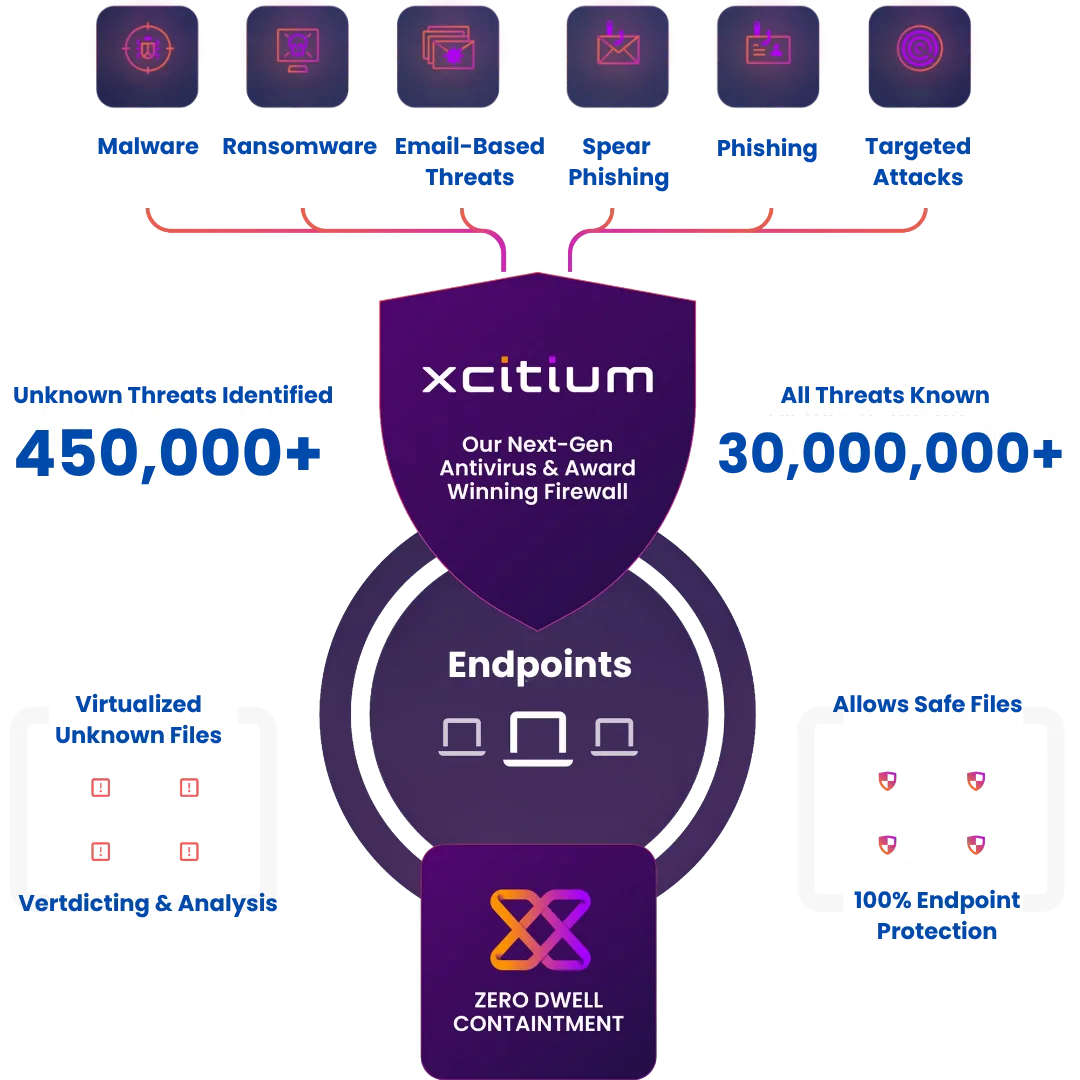
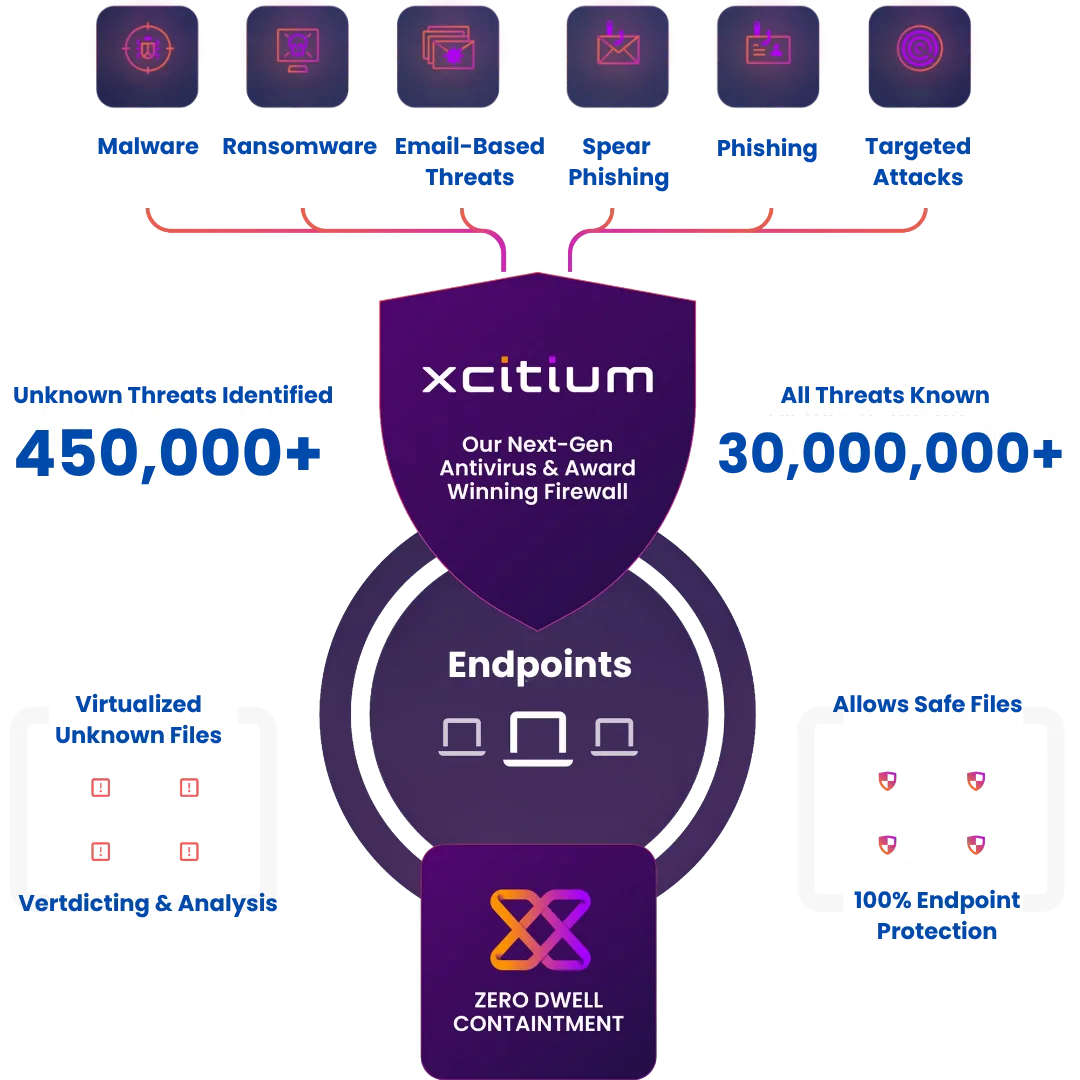
Move beyond detection-based security with Xcitium - a platform designed to prevent breaches, eliminate unknown threats, and secure your business without adding complexity.
Breach Prevention, Not Just Detection
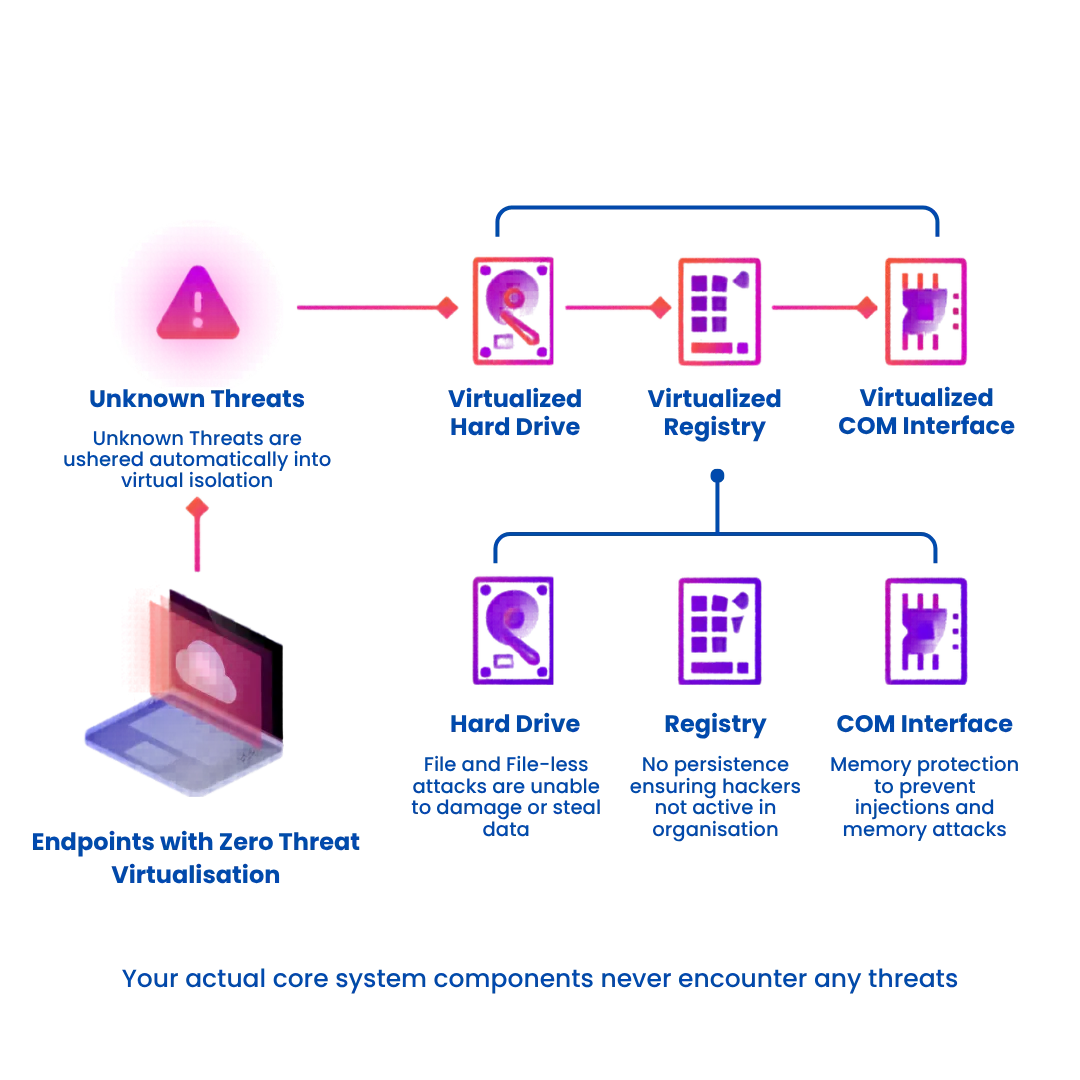
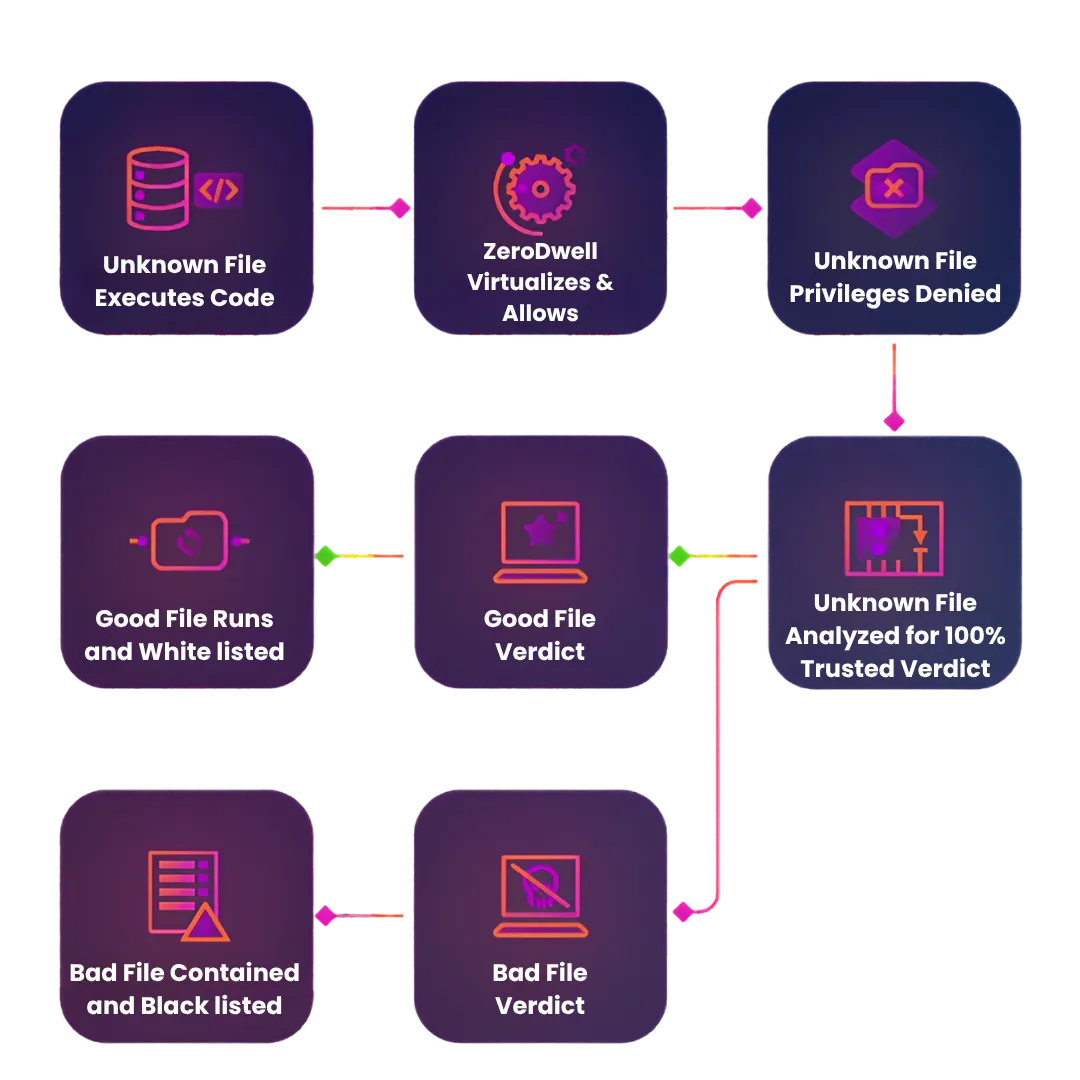
Traditional security reacts after threats enter your system. Xcitium’s ZeroDwell Containment approach prevents unknown files from executing, stopping attacks before they can cause damage.
Proven Protection Against Unknown Threats
Zero-day and fileless attacks are the biggest risk today. Xcitium isolates anything untrusted instantly, ensuring even unseen threats are neutralized without relying on signatures.
Unified Security Platform
No need to manage multiple tools. Xcitium brings antivirus, EDR, firewall, and threat intelligence together into a single, easy-to-manage solution — reducing cost and operational overhead.
Minimal Impact on Performance
Security shouldn’t slow your business down. Xcitium runs containment in the background, allowing users to work normally while threats are safely isolated.
Full Visibility & Faster Response
With real-time monitoring and advanced forensics, your IT team gets complete visibility into endpoint activity — enabling quicker investigations and smarter decisions.
Easy Deployment & Seamless Integration
Designed to fit into your existing infrastructure, Xcitium deploys quickly without disrupting workflows, making it ideal for growing businesses and enterprises alike.
Compliance & Risk Reduction
From data protection to regulatory requirements, Xcitium helps you stay compliant while significantly reducing your organization’s attack surface.

Prevent Breaches Before They Start with Xcitium
Xcitium is a next-generation endpoint security platform that stops threats before they execute. Using ZeroDwell Containment, it instantly isolates unknown files, preventing attacks without disrupting users.
With a unified approach combining antivirus, EDR, firewall, and AI-driven threat intelligence, Xcitium delivers complete protection across all endpoints. It integrates seamlessly into existing environments, providing real-time visibility, centralized control, and strong compliance — all while maintaining peak performance.

Core Elements Of Xcitium
Security Essentials For Real Time Protection
ZeroDwell Containment
Instantly Isolates Unknown Files To Block Threats Without Disrupting End Users.
Advanced Endpoint Protection
Protects Devices With Real-Time Monitoring, AI Analysis And Rapid Threat Response.
Cloud-Native Console
Manage Security Policies And Monitor Endpoints From A Unified Cloud Interface.
Threat Intelligence
Continuously Updated Threat Data Improves Detection And Response Accuracy.
Seamless Integration & Deployment
Quickly integrates into your existing IT infrastructure with minimal setup, allowing you to strengthen security without disrupting current workflows.
Advanced Forensics & Visibility
Gain deep insights into threats with detailed logs and forensic analysis, enabling faster investigation, smarter decisions, and stronger security posture.
Advanced Threat Protection That Goes Beyond Detection
Secure every endpoint with intelligent, prevention-first security powered by Xcitium — built to stop even the most sophisticated attacks before they cause damage.
ZeroDwell Containment
Automatically isolates unknown files and applications in a secure environment, ensuring threats are neutralized before they can execute or spread.
AI-Powered Threat Intelligence
Leverages continuously updated global threat data to identify, analyze, and respond to emerging threats with greater accuracy and speed.
Endpoint Detection & Response (EDR)
Provides real-time monitoring, behavioral analysis, and rapid incident response to detect and eliminate advanced and persistent threats.
Integrated Firewall Protection
Controls network traffic at the endpoint level, blocking unauthorized access and preventing lateral movement within your environment.
Advanced Malware & Ransomware Defense
Protects against zero-day attacks, fileless malware, and ransomware using layered security and behavior-based detection techniques.
Automated Threat Response
Reduces response time with automated actions, containment, and remediation — minimizing risk without manual intervention.

How Xcitium Stops Threats
Instant Containment Without Disrupting Your Endpoints
ZeroDwell Containment
Automatically Isolates Unknown Threats Before They Can Execute Or Spread.
Managed Detection & Response
24/7 Monitoring, Investigation And Response By Cybersecurity Experts.
Endpoint Protection Platform
Unified Platform Combines Antivirus, Firewall And Threat Prevention Tools.
Real Time Threat Intelligence
Leverages Global Data To Identify And Counter Emerging Cyber Threats Swiftly.
Incident Response Tools
Accelerates Investigation And Remediation Of Incidents Across All User Endpoints.
API Integrations
Seamlessly Connects With SIEM, SOAR And Other IT Security Systems.
Why GCC Leaders Choose Xcitium + Softriva Over Competitors?
| Key Factor | Xcitium + Softriva | Traditional Competitors |
|---|---|---|
| Security Approach | Prevention-first with ZeroDwell Containment — stops threats before execution | Detection-first — responds only after threats enter |
| Protection Against Unknown Threats | Automatically isolates unknown files — zero-day safe | Relies on signatures and behavior analysis — higher risk |
| Platform Architecture | Unified platform — AV + EDR + Firewall + Intelligence in one solution | Multiple tools with fragmented management |
| Operational Complexity | Centralized control with simplified management | Complex setups with multiple consoles |
| Performance Impact | Runs in the background without disrupting users | Can slow systems during scans and detection processes |
| Threat Response Time | Instant containment with automated response | Delayed response requiring manual intervention |
| Visibility & Forensics | Real-time insights with deep forensic analysis | Limited visibility or requires add-ons |
| Integration | Seamless integration with existing IT infrastructure | Often requires heavy reconfiguration |
| Compliance & Risk Reduction | Built-in support for compliance and audit readiness | Requires additional tools and processes |
| Cost Efficiency | Consolidated solution reduces tool and operational costs | Higher total cost due to multiple vendors |
| Local Expertise (Softriva) | GCC-focused implementation, support, and consulting | Limited regional understanding and support |
Active Defense for Endpoints
Stop Threats Before They Spread
Instant Threat Isolation
Automatically Quarantines Unknown Files For Real Time Threat Prevention.
No Downtime Assurance
Business Apps Stay Safe And Uninterrupted During Threat Containment.
Unified Threat Intelligence
Uses Global Data To Identify And Block Emerging Cyber Threats.


How Xcitium Stops Threats
Instant Containment Without Disrupting Your Endpoints
Enterprise Endpoint Protection
Detect Zero-Day Threats
Monitor in Real Time
Isolate Suspicious Applications
Enforce Policy Controls
Secure Remote Workforces
Protect Unmanaged Devices
Prevent Lateral Attacks
Encrypt Remote Connections
Enable Compliance Logging
Regulatory Compliance Readiness
Maintain Data Confidentiality
Achieve GDPR Alignment
Automate Audit Reporting
Prove Policy Enforcement
MSSP Security Offering
Multi Tenant Isolation
Scalable Deployment Options
Centralized Threat Monitoring
Custom Client Policies
Stop Threats Before They Become Breaches
Protect your endpoints with a prevention-first security approach that eliminates unknown threats, reduces risk, and keeps your business running without disruption.

STILL NOT SURE?
Frequently Asked Questions
What is ZetaHRMS and how does it simplify HR management?
ZetaHRMS is a cloud-based human resource management system designed for GCC businesses that automates payroll, attendance, recruitment, performance, and compliance, simplifying HR processes end-to-end.
Where can I download the ZetaHRMS mobile app for iOS and Android?
ZetaHRMS mobile apps are available on the Apple App Store for iOS devices and Google Play Store for Android devices. Search “ZetaHRMS” or use links provided by your organization.
How do I reset my ZetaHRMS login password?
Use the “Forgot Password” link on the ZetaHRMS login page. Enter your registered email to receive password reset instructions. Contact your HR administrator if issues persist.
What is Zeta ESS and how does employee self-service work?
Zeta ESS (Employee Self Service) allows employees to submit leave requests, view payslips, update personal info, and access HR documents through a secure mobile or web portal.
How do I activate my ZetaHRMS account using the activation URL?
Your HR department provides an activation URL via email. Click the link, set your password, and complete profile setup to activate access to ZetaHRMS.
Can I download the ZetaHRMS APK for offline installation?
ZetaHRMS APK files may be available from your HR or IT department for controlled offline installation on Android devices. Always use official or authorized sources to ensure security
Where can I find the official ZetaHRMS login page?
The official login page URL is typically shared by your employer or HR department and accessed via a secured company intranet or direct link provided during onboarding.
Does ZetaHRMS support multi-device access including mobile apps and web?
Yes, ZetaHRMS supports access via desktop web browsers and dedicated mobile apps on iOS and Android for flexible, on-the-go HR management.
How secure is my personal and payroll data on ZetaHRMS?
ZetaHRMS implements enterprise-grade security with encrypted data transmission, secure authentication, role-based access control, and compliance with data privacy standards including TDRA.
What steps are involved in downloading and installing the ZetaHRMS app APK?
Receive the APK file from your IT department, enable installation from unknown sources on your device settings, then run the APK installer. Confirm the app’s permissions and complete setup.
Is ZetaHRMS compatible with multiple currencies and regional compliance standards?
Yes, ZetaHRMS supports multi-currency payroll processing including AED, SAR, and USD, and complies with regional labor laws and tax regulations specific to GCC countries.
Can Softriva customize ZetaHRMS workflows to fit specific business needs?
Yes, Softriva works closely with clients to design and implement tailored approval chains, automated notifications, and integrations that fit unique organizational structures and HR policies.
How does Softriva ensure ZetaHRMS compliance with GCC regulations?
Softriva continuously monitors regional HR law changes and updates ZetaHRMS configurations accordingly, ensuring payroll accuracy, WPS compliance, data residency, and audit readiness for GCC businesses.

#4232 King Abdulaziz Rd
Albasatin District
Jeddah 23719
Saudi Arabia
+966 54 136 1317
Company
Managed Services
Web Solutions
Growth Hacking
Growth Tools
Business Tools
Copyright 2025. Softriva. All Rights Reserved.
