
Managed IT Services in Saudi Arabia: What You Get, What It Costs, and Why It Matters
Introduction
Most Saudi businesses do not have an IT problem. They have a risk management problem that expresses itself through IT.
Every business depends on its technology to function ,email, internal systems, customer databases, operational platforms, communication tools. When those systems work, they are invisible. When they fail, the cost is immediate: operations halt, staff are unproductive, clients cannot be served, and the business is exposed to data loss, security breaches, or compliance failures.
The traditional response to IT is reactive: something breaks, someone calls for help, the problem gets fixed. In a small business with basic technology, this approach is survivable. In a growing business with complex systems, multiple locations, or sensitive data, it is a meaningful liability.
Managed IT services replaces the break-fix model with something fundamentally different: a proactive, ongoing relationship in which your IT infrastructure is monitored, maintained, and optimized continuously ,and problems are identified and resolved before they impact your operations.
This guide explains what managed IT services actually includes, how it delivers value, what the Saudi market specifically requires, and what a high-quality managed services relationship looks like. It is written for business owners and operations leaders, not IT professionals ,the goal is to give you the information you need to evaluate your current IT arrangements and make better decisions.
The Real Cost of Reactive IT Support
The case for managed IT services is often made in terms of cost savings ,and the numbers are real. But the more persuasive case is about risk exposure. Consider what reactive IT actually costs:
Downtime cost: When a server fails, a security incident occurs, or a critical system becomes unavailable, every hour of downtime has a cost ,lost productivity, missed transactions, delayed deliveries, and in some cases reputational damage with clients who experience the failure. For a business with 20 staff at an average productivity value of SAR 200 per hour, a single half-day outage costs SAR 20,000 in lost productive time before any repair costs are counted.
Data loss exposure: Without a tested backup and recovery system, data loss is not a theoretical risk ,it is a certainty at some point. The cost of reconstructing lost business data, if it can be reconstructed at all, is significant. The cost of losing client data that cannot be recovered is potentially catastrophic and may trigger legal and regulatory consequences under Saudi PDPL.
Security incident cost: Cybersecurity incidents in Saudi Arabia are increasing in frequency and sophistication. The National Cybersecurity Authority has documented a consistent rise in attacks against Saudi businesses, particularly ransomware and phishing. The average cost of a cybersecurity incident for a mid-sized business includes the technical remediation, the operational downtime, the potential regulatory notification requirements, and the reputational impact with clients and partners.
Hidden staff time: In businesses without dedicated IT support, non-technical staff ,often senior staff ,spend significant time troubleshooting technology problems, coordinating with external vendors, and managing the anxiety of unreliable systems. This time is rarely measured but consistently present.
Managed IT services converts these unpredictable, high-impact costs into a predictable monthly investment that is almost always lower than the annualized cost of reactive support and downtime.
What Managed IT Services Actually Includes
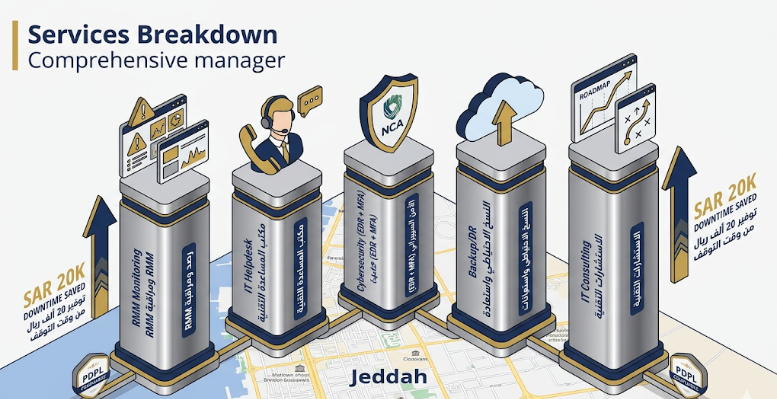
The term 'managed services' covers a range of service models, and the quality and coverage varies significantly between providers. Here is what a comprehensive managed IT service should include:
Remote Monitoring and Management (RMM)
RMM is the technical foundation of managed services. Software agents installed on your servers, workstations, and network devices continuously monitor system health ,CPU load, memory usage, disk space, network performance, security event logs, software patch status ,and alert the managed services team to anomalies before they become failures.
The value of RMM is in the word 'before.' A server running at 95% disk capacity will fail when it hits 100%. With RMM, that server is flagged when it hits 80%, additional capacity is provisioned, and the failure never occurs. Without RMM, you find out when everything stops.
Good RMM also automates routine maintenance tasks ,applying security patches across all devices during off-hours, running disk cleanup routines, restarting services that have hung ,that would otherwise require manual effort or would simply not be done.
IT Helpdesk Support
Helpdesk support covers the day-to-day technology issues your team encounters: a user cannot connect to the VPN, a printer is offline, an email account is not syncing, a software application is throwing an error. In a business without managed services, these issues are handled by whoever is most technically inclined ,often a non-IT senior staff member who loses productive time, or an external vendor who charges a call-out fee and takes hours or days to respond.
A good managed IT helpdesk provides defined response times (typically under one hour for business-critical issues), multiple contact channels (phone, email, ticketing system), bilingual support in Arabic and English, and documentation of every issue so that recurring problems are identified and resolved at their root cause rather than repeatedly patched.
Cybersecurity Management
Cybersecurity within a managed services framework is not a single product ,it is a layered set of controls that collectively reduce your exposure to threats:
Endpoint detection and response (EDR): Advanced security agents on every device that detect and respond to threats in real time, significantly more capable than traditional antivirus.
Email security: Filtering that catches phishing emails, malicious attachments, and business email compromise attempts before they reach your team's inboxes.
Firewall and network monitoring: Control of what traffic enters and leaves your network, with alerts on anomalous patterns.
Multi-factor authentication (MFA): Requiring a second verification step for access to critical systems, making stolen passwords alone insufficient for unauthorized access.
Security awareness training: Regular, brief training for your staff on how to recognize and respond to phishing and social engineering attempts ,because human behavior remains the most exploited attack vector.
Saudi Arabia's National Cybersecurity Authority has established a comprehensive cybersecurity framework ,the Essential Cybersecurity Controls ,that defines minimum security standards for organizations operating in the Kingdom. A managed services provider with Saudi market knowledge ensures your security posture meets these requirements.
Backup and Disaster Recovery
Backup is what you have. Disaster recovery is your ability to actually restore from it when you need to ,quickly enough to limit operational impact. These are two different things, and many businesses have the former without the tested capability for the latter.
A managed backup and disaster recovery service covers automated, regular backups of all business-critical data, secure offsite or cloud backup storage, periodic recovery testing to verify that backups actually restore correctly, and defined recovery time objectives (RTOs) and recovery point objectives (RPOs) that establish how quickly systems will be restored and how much data loss is acceptable.
The testing element is critical and frequently skipped in self-managed backup environments. A backup that has never been tested is a backup of unknown quality ,and you will only discover its quality at the worst possible moment.
IT Infrastructure Consulting and Roadmap
Beyond day-to-day support, a good managed services partner provides strategic guidance on your IT environment: identifying systems that are approaching end of life, recommending infrastructure improvements that improve performance or reduce cost, advising on technology procurement decisions, and helping you plan an IT investment roadmap that is aligned with your business objectives and growth trajectory.
For Saudi businesses navigating the technology requirements of Vision 2030 ,cloud adoption, digital service delivery, data compliance ,this advisory dimension of managed services is increasingly valuable.
What Saudi Businesses Specifically Need from a Managed IT Provider
The requirements for managed IT services in Saudi Arabia have specific characteristics that are not present in every market:
Saudi Data Protection Law (PDPL) Compliance
Saudi Arabia's Personal Data Protection Law, which came into full effect in 2023, imposes specific obligations on how businesses collect, store, process, and transfer personal data. Compliance requirements include data processing documentation, data subject rights management, data breach notification procedures, and restrictions on cross-border data transfers. A managed services provider operating in Saudi Arabia should be fully familiar with these requirements and should actively help you maintain compliance ,not leave it to you to navigate independently.
Arabic-Language Support Capability
Your staff are likely to be a mix of Arabic and English speakers. A helpdesk that only operates in English creates a support barrier for a significant portion of your team and reduces the effectiveness of the support function. Look for providers with genuine bilingual capability ,not just the ability to communicate in Arabic, but the technical vocabulary and cultural familiarity to provide effective support in both languages.
Local Physical Presence
Some IT issues require physical presence ,hardware failures, network infrastructure problems, on-site security incidents. A managed services provider based outside Saudi Arabia, or even in a different city within the Kingdom, has a response time disadvantage for on-site needs that can significantly impact downtime duration. For businesses in Jeddah, a Jeddah-based managed services team provides a response time advantage that remote providers cannot match.
Understanding of Saudi Business Operations
Saudi businesses have specific operational patterns ,Hijri calendar requirements in some systems, Arabic language interfaces for government-connected platforms, working week differences from Western markets, and the cultural context of business relationships that affects how IT support should be delivered and communicated. These are not obstacles for a provider embedded in the Saudi market; they are invisible background knowledge that shapes every interaction.
How to Evaluate a Managed IT Services Provider
Not all managed services providers are equal, and the differences that matter most are not always visible in a sales presentation. Here is how to evaluate providers substantively:
Ask for their technology stack: A serious managed services provider uses professional-grade RMM, security, and backup platforms ,not consumer tools. Ask them to name the specific platforms they use for monitoring, endpoint security, backup, and helpdesk ticketing, and research those platforms independently.
Request their SLA documentation: Service level agreements should define specific response and resolution times for different issue categories, the escalation process when issues are not resolved within SLA, the remedies available when SLA commitments are missed, and the monitoring and reporting mechanism that demonstrates SLA compliance.
Check their cybersecurity credentials: Ask about their experience with the NCA Essential Cybersecurity Controls framework, their cybersecurity incident response process, and whether they have managed a security incident for a Saudi client. The answers reveal whether cybersecurity is genuinely integrated into their service or is a sales-layer addition.
Speak with reference clients in similar industries: The most valuable reference conversation is with a client who has been through a significant IT incident ,a security event, a server failure, a data loss situation ,while under managed services. How the provider responded in that moment tells you far more than any standard client satisfaction reference.
5. Understand their offboarding process: A provider who makes it difficult to leave is one that knows their service will not keep you without contractual friction. Ask specifically how data is transferred and access is revoked if you choose to change providers. The answer is a proxy for their confidence in their service quality.
Key Takeaways
✓ Reactive IT support costs Saudi businesses more in downtime, staff time, and security exposure than managed services ever will ,the economics favor proactive management.
✓ Comprehensive managed IT includes RMM, helpdesk, cybersecurity, backup and disaster recovery, and strategic advisory ,not just helpdesk tickets.
✓ Saudi PDPL compliance, Arabic-language support, and physical local presence are specific requirements of the Saudi market that not all providers can meet.
✓ Backup and disaster recovery are two different things ,having backups without tested recovery capability leaves your business exposed.
✓ Evaluating a managed services provider should focus on their technology stack, SLA specificity, cybersecurity credentials, and reference quality ,not just price.
✓ The Saudi National Cybersecurity Authority's Essential Cybersecurity Controls framework defines minimum security standards that your managed IT provider should actively help you maintain.
Frequently Asked Questions
Q: What is the typical cost of managed IT services for a Saudi SME?
A: Managed IT services pricing in Saudi Arabia typically ranges from SAR 200 to SAR 800 per user per month, depending on the scope of services, the number of devices covered, the level of cybersecurity included, and the response time commitments in the SLA. For a 20-person business, this translates to roughly SAR 4,000 to SAR 16,000 per month. This should be compared against the fully loaded cost of reactive IT support ,including call-out fees, downtime cost, and staff time managing IT issues ,which consistently exceeds managed services investment for businesses beyond a certain complexity threshold.
Q: Can we use managed services alongside our existing internal IT staff?
A: Yes, and this is a common model. Many Saudi businesses have one or more internal IT staff who handle day-to-day user requests and internal projects, with a managed services provider providing the monitoring infrastructure, security management, backup systems, and specialist expertise that is impractical to maintain in-house. This co-managed model typically delivers better outcomes than either approach in isolation ,the internal staff have the business context, the managed services provider has the technical depth and tooling.
Q: How quickly can managed services be set up for our business?
A: A standard managed services onboarding ,including discovery, RMM agent deployment, security tooling configuration, backup setup, and helpdesk account creation ,typically takes two to four weeks for an SME and four to eight weeks for a larger organization with more complex infrastructure. The timeline depends primarily on the complexity of your existing systems and the availability of your internal team for the onboarding process.
Q: What happens to our data if we switch managed IT providers?
A: This should be explicitly addressed in your contract before you sign. You own your data, and any managed services provider should have a documented, contractually committed process for returning all data and revoking all system access at the end of the engagement. Ask for this documentation in writing during the contract stage. Any provider unwilling to commit to clear data return and access revocation procedures should be treated with significant caution.
Q: Is cybersecurity a separate service or part of managed IT?
A: In a properly structured managed services engagement, cybersecurity is integrated ,it is not a separate line item you bolt on after the fact. Security monitoring, patch management, endpoint protection, and email security should all be part of the core managed services scope. Some providers offer tiered packages where higher cybersecurity coverage is available at higher price points, which is a reasonable approach as long as the baseline tier provides meaningful protection and the higher tiers genuinely add depth rather than just adding cost.
Conclusion
The question for Saudi businesses is not whether to invest in managed IT services ,it is how quickly they can make the shift from reactive to proactive IT management, and what that shift will cost versus what the status quo is currently costing.
The Saudi market adds specific dimensions to this decision: an evolving regulatory environment with PDPL compliance requirements, a growing cybersecurity threat landscape that the National Cybersecurity Authority has specifically flagged, and the operational demands of a rapidly digitizing economy where systems downtime has an increasingly direct impact on business outcomes.
The businesses that manage this transition well share common characteristics: they chose a provider with genuine Saudi market knowledge rather than a generic IT vendor, they insisted on specific SLA commitments rather than general assurances, they integrated cybersecurity into the managed services scope from the beginning rather than treating it as an afterthought, and they established a strategic advisory relationship with their provider rather than treating managed services as a pure operational function.
Softriva has been delivering managed IT services to Saudi businesses since 2006. Our team is based in Jeddah, operates in Arabic and English, and brings deep familiarity with the Saudi regulatory environment and technology landscape. We offer a free IT infrastructure audit as the starting point for every managed services engagement ,a comprehensive review of your current systems, security posture, and backup arrangements, with a clear prioritized improvement plan.
